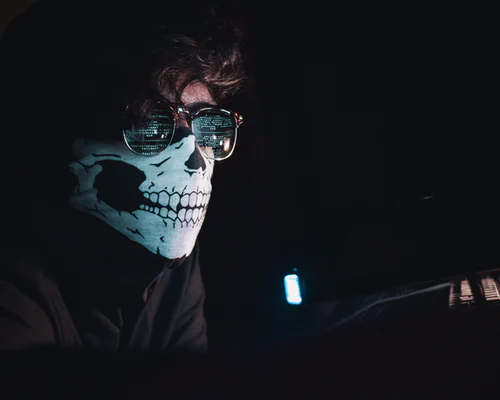
Welcome to the 21st century, where an attack could be online; a hack is a breach of system security, and a virus affects computer systems and networks rather than living beings. Technology is constantly evolving, with technological advancements and breakthroughs happening at least once a year. This constant evolution, though highly beneficial, also poses threats. With the digital scenario evolving, avenues for security breaches also increase. Thus, organizations and government bodies have to upgrade their security framework for efficient management and security constantly. This constant surveillance and up-gradation are called Attack Surface Management.
Today’s digital scenario calls for an entirely different security measure set up, as people are more susceptible to online attacks than offline. Data is the currency in this age, and there are quite a few malicious entities who try to obtain data illegally and by force. Large companies and organizations use the best security systems available to safeguard their data online. Governments, MNCs, start-ups and even individuals have some form of data online, and this data is at potential risk.
An attack surface is the total of all potential vulnerabilities in a system network. While organizations will have several protocols to keep their data in check, hackers and other entities can still try and gain access to it by every means possible. When the security protocols are not updated constantly, it becomes even more accessible for them to obtain this data. Therefore, constant surveillance of all protocols and data storage servers is necessary to prevent these attacks. This continuous surveillance helps organizations shore up potential leaks and strengthen/update their firewalls and other digital security methods; this is attack surface monitoring.
EFFICIENTLY MANAGING ATTACK SURFACES
Attack surface management is an intricate and never-ending process. Constant vigilance is the only solution to ensuring there are no exploitable avenues or vulnerabilities for external forces to get into the system. These vulnerabilities are of two types,
- Physical – Physical vulnerabilities are the weak points or breach points in a device, for example, a PC, laptop, phone, etc. Weak security software, outdated software, failure to follow protocol, human error, etc., are some of the vulnerabilities a physical device poses.
- Digital – Digital vulnerabilities are exploitable weak points in a network’s hardware or software. This vulnerability is more large-scale and entirely dependent on the amount of code run by the organization. Digital vulnerability refers to the system network as a whole rather than a single device.
An organization must constantly monitor both its physical and digital assets and security protocols to detect any threat and nullify it immediately. Large organizations and government bodies usually run enormous amounts of code on their network; the larger the code, the higher the chance of vulnerability. The coding has to be airtight to ensure there are no chances of external sources exploiting any weak points to get inside. It is why engaging the services of a digital security agency is highly beneficial. They constantly monitor the attack surfaces and prevent threats before they occur.
The first step is to identify potential weaknesses in the system framework; this is attack surface mapping. This exercise allows the agency to identify potential threats and vulnerabilities and thus map the attack surface. Once they recognize the possible danger or the attack surface, the agency analyzes it. This attack surface analysis allows them to understand the different avenues that an external source can exploit to get into the system. Once they sufficiently analyze the attack surface, they can efficiently upgrade the security protocols to deter such attacks.
Additionally, a digital security agency also helps in attack surface reduction. They maximize the features of the security framework and related software to reduce the potential of threats actively. They provide services of constantly monitoring digital and physical assets for possible breaches and give real-time alerts if any vulnerability is detected. Their services effectively reduce attack surface visibility by continually monitoring and nullifying online security threats.
An online security agency does a thorough, in-depth and wholesome analysis of an organization’s digital and physical infrastructure. Their software runs in the background, constantly perusing through domains, sub-domains, servers, etc., to identify potential security vulnerabilities. The software then alerts the organization about these vulnerabilities, if any, so that they are immediately resolved. This speedy action, along with the constant monitoring, stops the exploit before it occurs.
An attack surface management tool offers a prime advantage in today’s digital scenario. With hackers constantly trying to breach organizations and government bodies, this tool/software ensures minimal exploitation. Malicious external sources always look out for any weak spots in an organization’s security framework to take advantage of it for personal reasons. This tool ensures that no external sources can get into the organization’s framework today or in the future.